Checklist for Deploying Elastic Defend (XDR)
Elastic Defend has matured into a serious endpoint and extended detection and response capability within the Elastic ecosystem. It promises visibility across endpoints, workload telemetry, and security analytics in one place. Yet deployment is rarely straightforward. Many organisations underestimate the operational shift involved. They focus on agent rollout and miss the deeper preparation work that determines whether the platform delivers clarity or noise.
A practical checklist for deploying Elastic Defend (XDR) needs to go beyond installation steps. It should reflect infrastructure reality, user behaviour, and internal process gaps. This is where most friction appears.
Understand the Environment Before Touching the Agent
Elastic Defend does not operate in isolation. It sits on top of Elastic Stack components, ingest pipelines, index lifecycle policies, and integration frameworks. If those foundations are inconsistent, the XDR layer will amplify the weakness.
Begin with asset clarity. Not a spreadsheet last updated two years ago. A living view of endpoints across Windows, macOS, Linux, cloud workloads, and remote devices. Many deployments stall because teams discover unmanaged servers halfway through rollout.
Network topology matters as well. Elastic Agents require stable connectivity to Fleet and Elasticsearch nodes. Remote sites with restricted outbound rules can create silent data gaps. These gaps only surface during incident response. By then, it is too late.
Version alignment also deserves attention. Mismatched stack versions create instability that security teams mistake for product weakness. Before deploying at scale, confirm compatibility across Elasticsearch, Kibana, Fleet Server, and agents. A checklist for deploying Elastic Defend (XDR) that skips this groundwork becomes an operational risk.
Define Detection Intent Before Enabling Rules
Elastic provides a rich library of prebuilt detection rules. Enabling them all on day one looks decisive. In practice, it floods analysts with alerts that have not been tuned for the organisation’s baseline.
Detection intent should come first. What threats are most relevant to the business model? Credential theft in a financial services environment demands closer attention than commodity crypto mining. A manufacturing firm may prioritise lateral movement inside segmented operational networks.
Without this clarity, teams end up reacting to what the system surfaces rather than what actually matters.
Baseline normal behaviour before expanding detection depth. Capture process execution patterns. Observe administrative scripts. Identify legacy applications that behave suspiciously but are business critical. This period often reveals that the risk lies in internal tooling rather than external adversaries.
Elastic Defend is capable of behavioural protection, but behavioural engines require context. That context comes from disciplined observation.
Architecture Planning and Data Flow
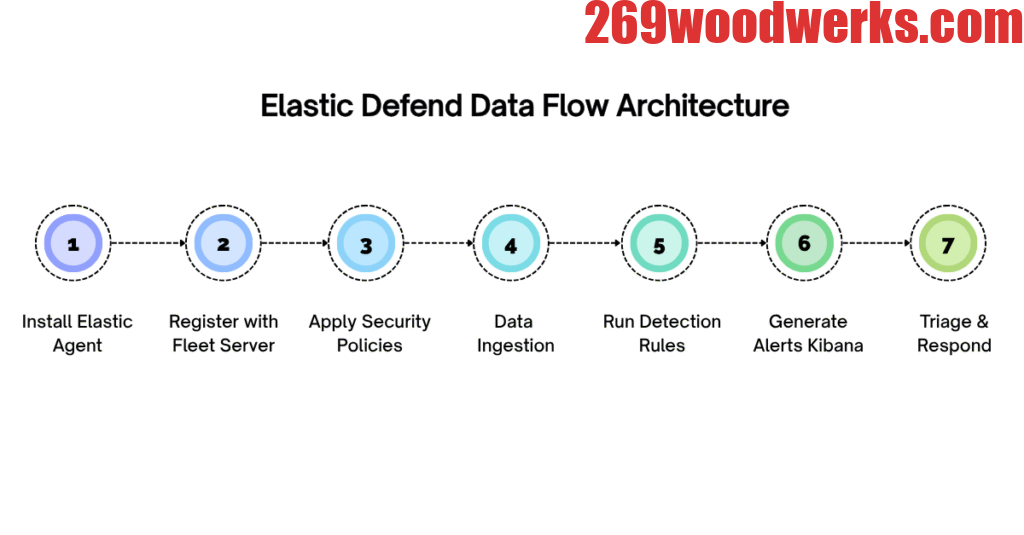
Before expanding the deployment, it helps to visualise how the components interact.
The following outline illustrates a typical data and control flow within an Elastic Defend deployment:
- Endpoint installs Elastic Agent
- Agent registers with Fleet Server
- Fleet Server applies security integration policies
- Telemetry flows into Elasticsearch
- Detection rules analyse indexed data
- Alerts surface in Kibana Security
- Analysts triage and respond
Each step appears simple in isolation. The complexity emerges at scale.
Endpoint enrolment must handle certificate validation and authentication securely. Fleet Server requires resilience and load balancing if thousands of agents report concurrently. Elasticsearch clusters must absorb telemetry spikes during malware outbreaks or patch cycles. Detection rule performance can degrade if index tuning is neglected.
Treat this flow as an operational chain. Weakness in one link cascades across the system.
Agent Rollout Strategy
Blind mass deployment often leads to disruption. Security agents interact deeply with operating systems. Kernel level visibility and behavioural controls can interfere with fragile legacy applications.
A phased rollout reduces risk. Start with a technically mature pilot group. Include devices with varied roles, not only developer laptops. Servers running line of business systems often surface unexpected compatibility issues.
Performance monitoring during pilot deployment is critical. CPU spikes, memory overhead, and disk IO patterns should be recorded and compared to baseline metrics. Security teams sometimes dismiss performance complaints as resistance. In several environments, the complaints have been valid.
Policy granularity deserves attention. Not all endpoints require identical protections. Domain controllers, developer workstations, and kiosk systems operate differently. Applying uniform policies increases false positives and operational friction.
Elastic Defend allows policy customisation. Use it deliberately.
Log Retention and Storage Planning
Extended detection implies extended data retention. Many organisations enable detailed telemetry without calculating storage impact. Elasticsearch clusters expand rapidly under endpoint event volume.
Retention policies must align with investigation needs and regulatory obligations. Retaining thirty days of high-fidelity endpoint telemetry may suffice for some sectors. Others require longer windows for compliance audits.
Index lifecycle management should be configured early. Hot, warm, and cold tier strategies can reduce cost without sacrificing investigative capability. Without this planning, storage cost becomes the reason leadership questions the entire XDR investment.
Security telemetry is valuable only if it remains searchable and reliable. Index corruption or cluster instability during peak investigation periods erodes trust quickly.
Incident Response Integration
Deploying Elastic Defend is not the same as improving security posture. Improvement depends on how alerts feed into response processes.
Clarify escalation paths. Decide which alerts trigger automated containment. Elastic allows host isolation and response actions, but automation without governance introduces risk. Isolating the wrong server during business hours can cause serious disruption.
Integration with existing ticketing systems should be tested before going live. Alert routing failures create blind spots. Analysts may assume someone else is reviewing high severity alerts.
Run tabletop exercises after deployment. Simulate ransomware execution or privilege escalation scenarios. Observe how quickly analysts navigate the interface, identify root cause, and coordinate containment. These exercises often reveal that technical deployment succeeded, yet operational readiness lags behind.
Continuous Tuning and Drift Control
No deployment remains static. Operating systems update. New applications appear. Threat actors adapt.
Regular rule review sessions help maintain relevance. Disable noisy detections that add little value. Adjust thresholds based on actual behaviour rather than vendor defaults.
Monitor agent health actively. Agents silently failing to check in are common in distributed environments. Without health dashboards and alerting on inactive agents, coverage gaps widen unnoticed.
Over time, policy drift creeps in. Emergency exclusions made during incidents sometimes remain permanently. A periodic review of exclusions prevents security erosion.
A checklist for deploying Elastic Defend (XDR) should treat tuning as ongoing work, not post deployment housekeeping.
Governance and Ownership
Ownership ambiguity weakens even well deployed platforms. Determine who owns policy changes. Define who approves rule modifications. Separate administrative rights where possible.
Audit logging within the Elastic environment should be enabled to track configuration changes. In complex organisations, security engineering and operations teams may both interact with the platform. Clear accountability avoids internal friction during investigations.
Reporting to leadership also needs consideration. Executives rarely require detailed detection logs. They need trend visibility, risk indicators, and clarity on coverage. Dashboards should reflect this distinction rather than mirror analyst views.
Governance does not slow deployment. It prevents long term disorder.
Human Factors Often Overlooked
Technology decisions tend to overshadow behavioural realities. Analysts require time to learn the Elastic interface deeply. The platform is powerful but dense. Without structured exposure, teams use only a fraction of its capability.
Training should not focus solely on features. It should centre on investigative workflows. How to pivot from process ancestry to network activity. How to correlate endpoint alerts with authentication logs. These habits build confidence.
Cultural resistance may also surface. Some IT teams perceive endpoint monitoring as surveillance. Transparent communication about intent and data scope reduces tension.
Security controls succeed when people understand them.
Conclusion
Elastic Defend can deliver strong endpoint visibility and behavioural detection when deployed with care. Rushing deployment creates noise and distrust. Thoughtful preparation, phased rollout, and disciplined tuning turn it into a stable operational asset.
For organisations navigating this complexity, external guidance can reduce friction and shorten stabilisation time. CyberNX are a reliable elastic stack services partner. They can help you maximize your investments and implement Elastic services according to best practices on elastic cloud, on-premises, or public cloud to meet your business requirements. Security platforms reveal their true value during incidents. Deployment decisions made quietly at the beginning determine how those moments unfold.
Disclaimer
The information presented in this article is intended for general informational purposes only and does not constitute professional cybersecurity, legal, or compliance advice. Every organisation’s IT environment, risk profile, and regulatory requirements are different, and the deployment of Elastic Defend (XDR) should be planned and executed in consultation with qualified security professionals. While efforts have been made to ensure accuracy and relevance, no guarantee is provided regarding completeness or suitability for specific use cases. Readers are advised to perform independent assessments and validations before implementing any security solutions or architectural changes.